Why America Must Redesign Strategy for a World of Converging, Transregional Wars
By Dr. Isaiah (Ike) Wilson III
Introduction: The War Already Underway
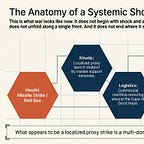
In the early hours of a recent morning, a cluster of commercial vessels slowed unexpectedly in the southern Red Sea. Insurance premiums had already surged. Satellite imagery showed unusual patterns of maritime rerouting. Within hours, a Houthi missile strike—launched from Yemen but enabled by Iranian support networks—forced another wave of global shipping to divert around the Cape of Good Hope. The immediate damage was limited. No fleets clashed. No formal declarations were issued.
And yet, the effects rippled outward almost instantly.
Energy markets reacted. European supply chains tightened. U.S. naval assets surged into position. Insurance firms recalibrated risk models. Online, competing narratives emerged—some framing the attack as resistance, others as escalation, all shaping perception in real time. What appeared, at first glance, to be a localized proxy strike quickly revealed itself as something far more consequential: a multi-domain disruption with global systemic effects.
This is what war looks like now.
It does not begin with shock and awe. It does not unfold along a single front. And it does not end where it starts.
The United States is already engaged in such conflicts—against Iran, against Russia, against a broader ecosystem of state and nonstate actors—but it continues to treat them as discrete crises rather than as manifestations of a single, evolving condition.
That condition is compound security competition: a form of strategic interaction in which adversaries apply synchronized pressure across military, economic, informational, and political domains, producing effects that are not merely additive but convergent and contagious.
The Red Sea disruption is not an isolated incident. It is a node in a wider system. It connects to proxy networks in Iraq and Lebanon, to cyber activity targeting infrastructure, to energy markets in Europe, and to political debates in Washington. It is part of a conflict that is already underway—one that is persistent, distributed, and largely unrecognized for what it is.
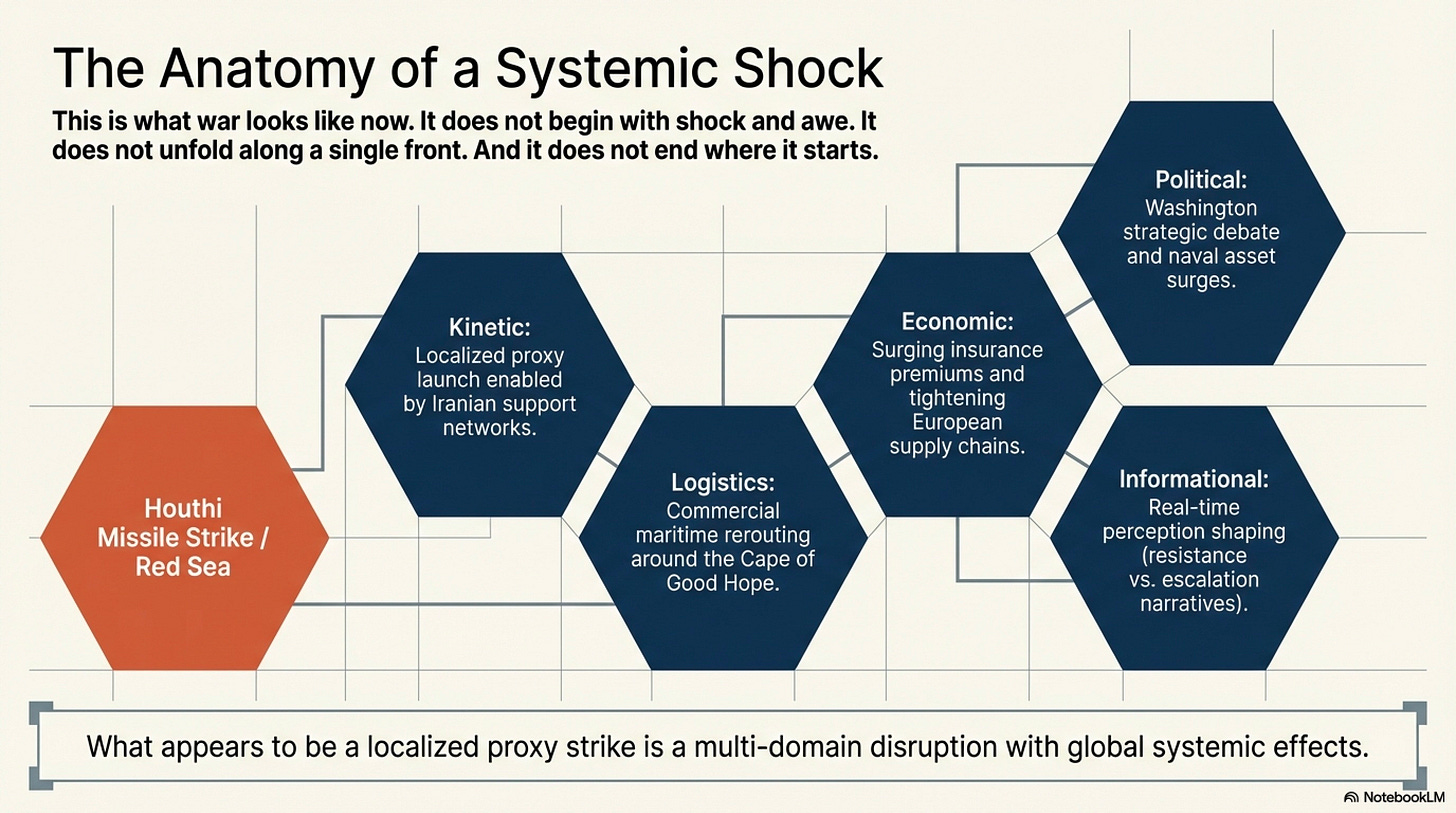
The danger is not simply that the United States is underestimating these events. It is that it is misunderstanding their structure.
For decades, American strategy has been built on the assumption that threats can be bounded, that wars can be deterred through clear signaling, and that escalation follows a recognizable ladder. But in a world of converging systems, those assumptions no longer hold.
The challenge is no longer to deter a single adversary in a single domain. It is to operate effectively within a complex, interconnected battlespace in which actions in one arena reverberate across many others.
The task, therefore, is not merely to respond to events, but to understand—and ultimately shape—the system in which those events occur.
The End of Linear War
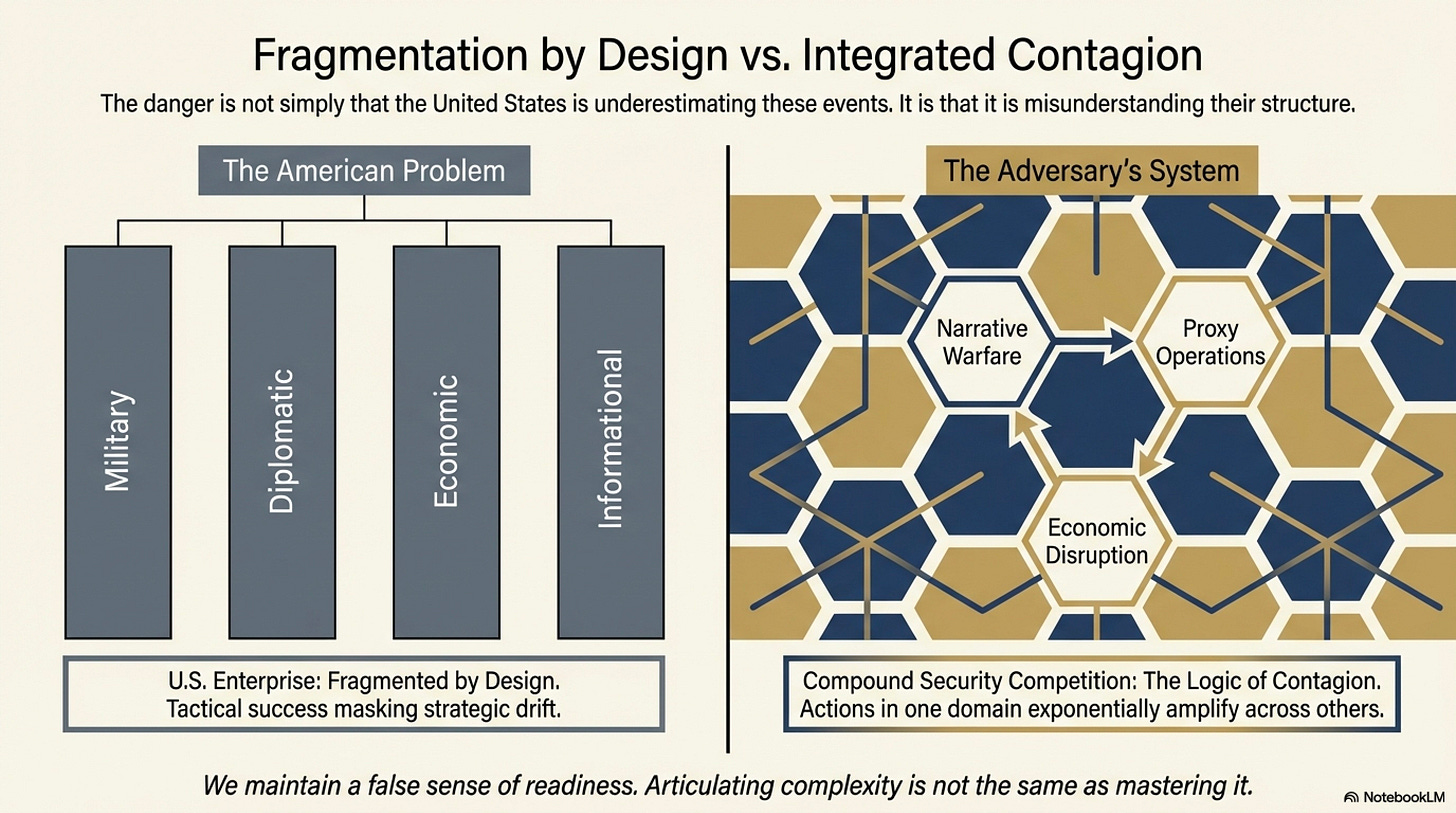
For much of the post–Cold War era, U.S. national security strategy has rested on a set of assumptions that, while once useful, now obscure more than they reveal.
Policymakers have tended to treat conflicts as bounded in space and time, threats as discrete and attributable, and war as a phenomenon that escalates visibly and concludes decisively. These assumptions have shaped not only how the United States fights, but how it plans, organizes, and even thinks about competition itself.
Yet the strategic environment has shifted in ways that render these assumptions increasingly obsolete.
The United States now operates in a world defined less by isolated crises than by compound security competition—a condition in which adversaries employ multiple instruments of power simultaneously across domains and regions, producing effects that are interconnected, reinforcing, and often nonlinear. As Thomas Schelling once suggested, the essence of strategy lies in shaping the opponent’s expectations; today, however, the challenge is more fundamental: it is to understand the system in which expectations themselves are formed and manipulated.¹
In such an environment, war does not begin with a clear rupture, nor does it end with a decisive event. Instead, it unfolds as a continuous process of interaction—persistent, ambiguous, and cumulative. The problem for the United States is not simply that threats have multiplied, but that they now converge, creating dynamics that cannot be understood—or managed—through traditional frameworks of deterrence and response.
From Capabilities to Conduct
A central insight of this new strategic reality is that the traditional focus on capabilities—on counting forces, platforms, and weapons systems—is no longer sufficient. What matters increasingly is not what adversaries possess, but how they behave. The analytical shift toward understanding “sources of conduct”—motive, intent, opportunity, and risk perception—marks a critical evolution in strategic thinking.²
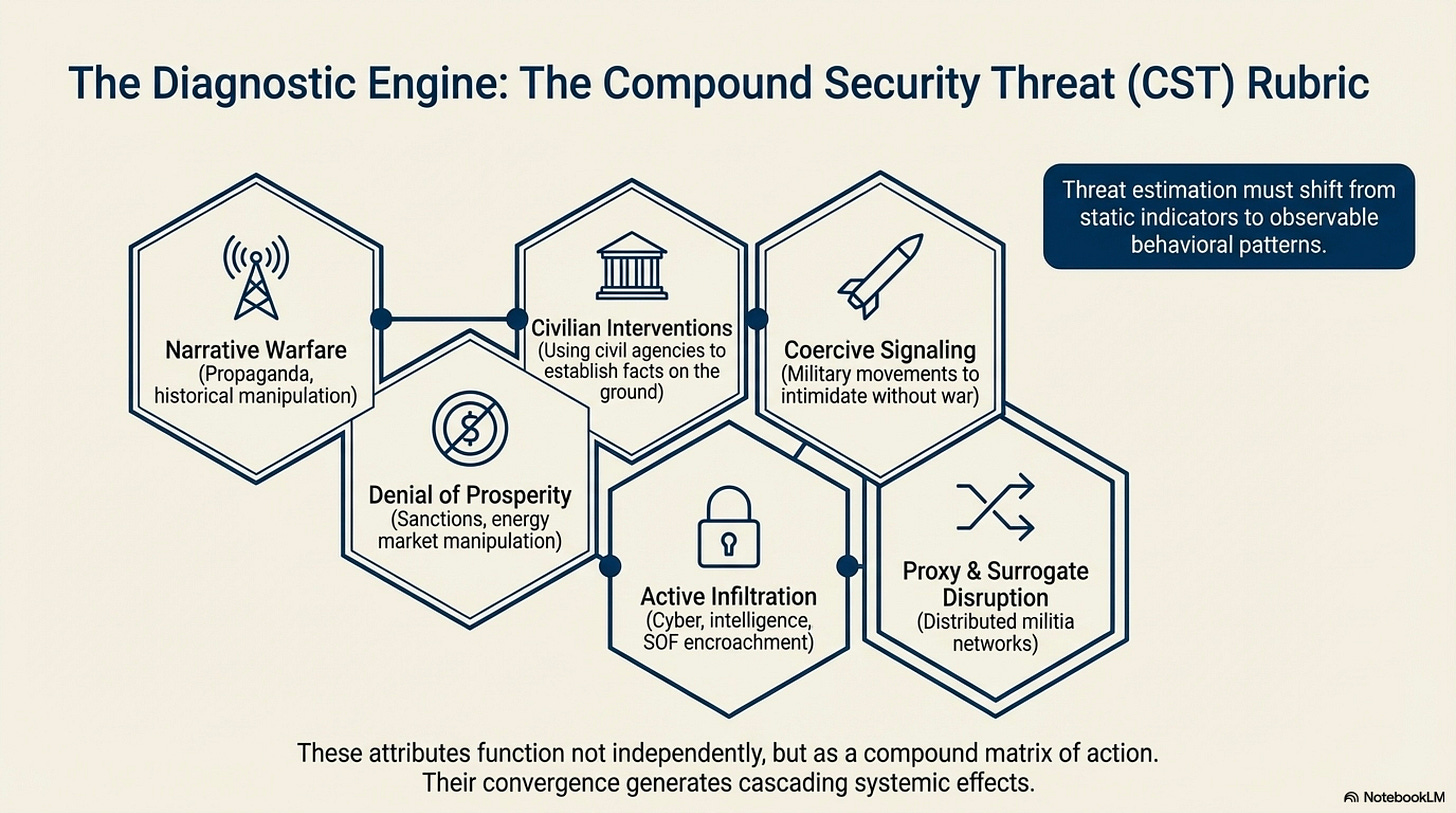
Seen through this lens, modern rivalry reveals a recurring pattern of behavior. Adversaries such as China, Russia, and Iran do not rely on singular forms of coercion. Instead, they operate through a repertoire of integrated actions: narrative warfare designed to shape perception, economic measures aimed at constraining prosperity, cyber and informational intrusions that destabilize systems, and proxy operations that extend reach while preserving deniability. These actions are not episodic. They are coordinated.
This behavioral integration reflects what might be called a new grammar of conflict. As Sun Tzu observed, the supreme art of war is to subdue the enemy without fighting; in the contemporary environment, this principle has been expanded and operationalized across domains, producing a form of competition that is both persistent and difficult to attribute.³ The result is not the absence of war, but its transformation.
The Logic of Compounding: From Interaction to Contagion
What distinguishes this new form of competition is not merely its breadth, but its structure. The defining characteristic of compound security is interaction. Actions taken in one domain do not remain confined; they propagate, intersect, and amplify across others. Economic coercion reshapes political legitimacy. Cyber intrusions enable proxy operations. Narrative campaigns alter the meaning of military signaling. Each domain becomes both cause and effect.
This dynamic produces outcomes that are not additive but exponential. As Henry Kissinger has warned, the contemporary international system is entering a phase in which complexity itself becomes a source of instability.⁴ In such a system, small perturbations can generate cascading effects, and local conflicts can acquire global significance through pathways of interdependence.
The consequence is a form of conflict best understood as contagion. Pressure applied in one location can trigger reactions across multiple regions, creating feedback loops that sustain and intensify competition. The strategic challenge, therefore, is not simply to counter individual actions, but to understand and shape the system of interactions that gives rise to them.
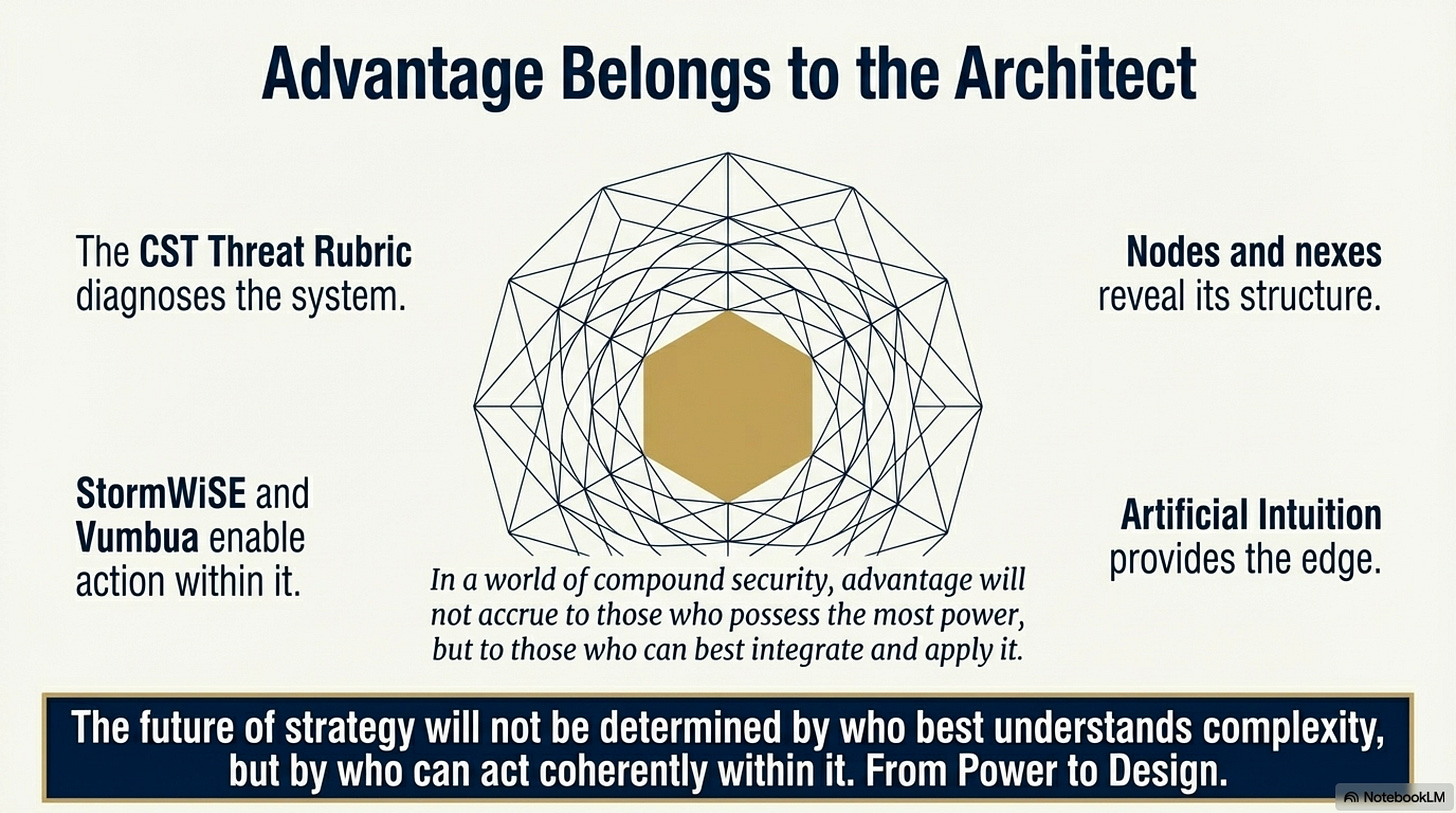
Nodes, Nexes, and the Geography of Convergence
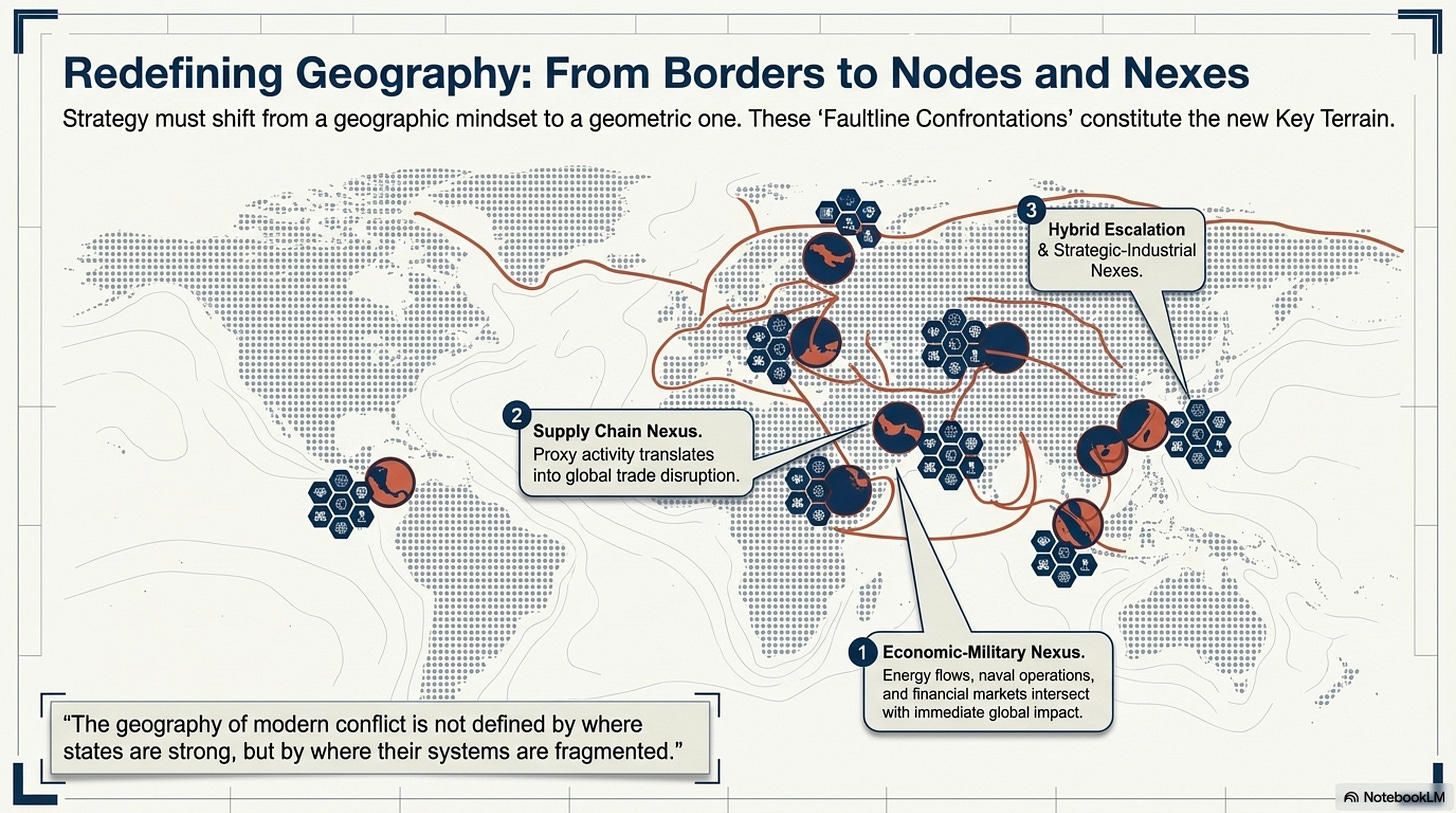
To grasp how compound dynamics operate in practice, it is necessary to rethink the geography of conflict. Traditional strategic maps, organized around regions and theaters, fail to capture the reality of a world structured by intersections rather than boundaries. What matters are not simply locations, but points of convergence—what might be termed nodes and nexes.
Nodes represent discrete sites of activity: ports, financial centers, communication networks. Nexes, by contrast, are the points at which multiple forms of pressure intersect, producing compound effects. It is at these nexes—often located in border regions, chokepoints, or governance gaps—that the dynamics of modern competition are most visible and most consequential.
Crucially, these nexes are not accidental. They are often the product of institutional design. As organizational theorists such as Amy Zegart have shown, bureaucratic structures can generate vulnerabilities by creating seams between authorities and functions.⁵ In the contemporary strategic environment, adversaries exploit these seams deliberately, operating in the spaces where U.S. and allied systems are least integrated.
The implication is stark: the geography of modern conflict is not defined by where states are strong, but by where their systems are fragmented.
A Comparative Vignette: Russia, Ukraine, and the Anatomy of Compound War
The ongoing war in Ukraine offers a vivid illustration of these dynamics. Although often framed as a conventional conflict between two states, the war is, in fact, a deeply compound phenomenon. Russia’s approach has combined conventional military force with cyber operations, energy coercion, disinformation campaigns, and proxy activities, creating a multidimensional strategy aimed at both battlefield outcomes and systemic disruption.
Ukraine’s response, supported by Western allies, has likewise reflected a compound approach. Military resistance has been complemented by narrative strategies that mobilize international support, economic measures that target Russian vulnerabilities, and technological innovations that enhance resilience. The war has thus become not only a contest of arms, but a contest of systems.
What is particularly striking is the way in which the conflict has generated transregional effects. Energy disruptions have reshaped European markets. Food supply shocks have affected global stability. Information campaigns have influenced political discourse far beyond the immediate theater. As Lawrence Freedman has noted, the war demonstrates how modern conflicts can “spill over into every aspect of international life.”⁶
In this sense, Ukraine is not an exception but a prototype—a clear example of how compound security competition operates in practice.
Iran and the Structure of Compound Contagion War
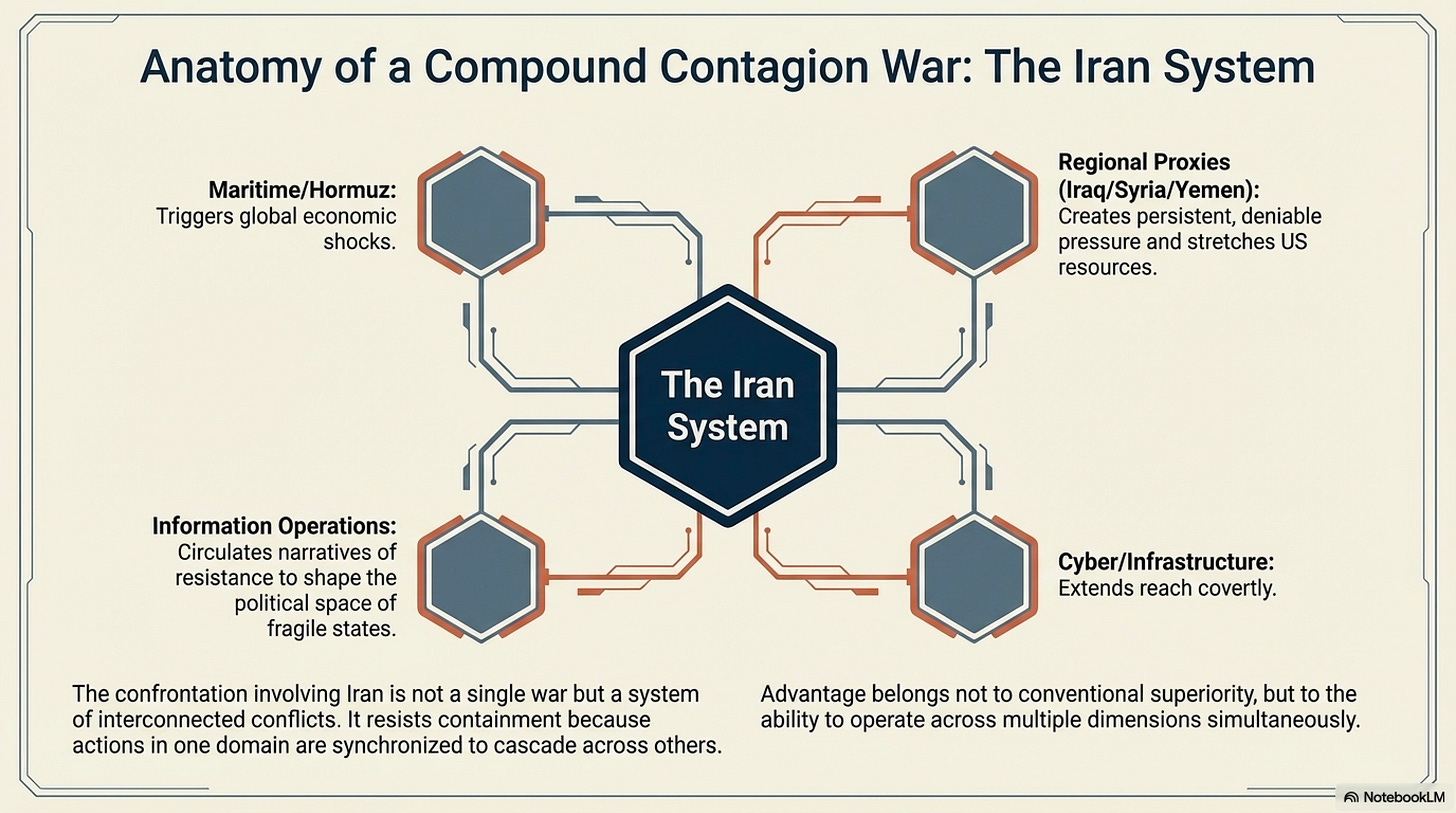
If Ukraine illustrates the dynamics of compound conflict in a largely conventional setting, Iran represents its most fully developed form in a transregional context. The confrontation involving Iran is not a single war but a system of interconnected conflicts, spanning multiple regions and domains.
Iran’s strategy is built on integration. Through networks of proxies across the Middle East, maritime operations in critical chokepoints, cyber activities targeting infrastructure, and sustained narrative campaigns, Iran has constructed a distributed system of influence and coercion. Each component reinforces the others, creating a resilient and adaptive structure.
The key to understanding this system lies in its synchronization. Actions in one domain are timed and calibrated to produce effects in others, generating a form of strategic depth that is difficult to counter. As Kenneth Pollack has argued, Iran’s strength lies not in conventional superiority, but in its ability to operate across multiple dimensions simultaneously.⁷
The result is a form of compound contagion war—a condition in which localized actions generate cascading regional and global effects. Traditional approaches, focused on discrete threats or theaters, are ill-suited to address such a system.
The American Problem: Fragmentation by Design
If adversaries have adapted to this environment, the United States has been slower to do so. The core problem is not a lack of capability, but a lack of integration. The U.S. national security enterprise remains organized around separations—between agencies, between domains, and between regions—that reflect an earlier era.
This fragmentation has profound consequences. It produces gaps in planning, delays in response, and inconsistencies in execution. More importantly, it creates the very seams that adversaries exploit. As the experience of the past two decades has shown, the United States can achieve tactical success while falling short of strategic objectives—a paradox rooted in the disjunction between how it fights and how it organizes.⁸
Addressing this problem requires more than incremental reform. It requires a fundamental rethinking of how strategy is conceived and implemented.
Integration in Practice: Lessons from the JIATF Model
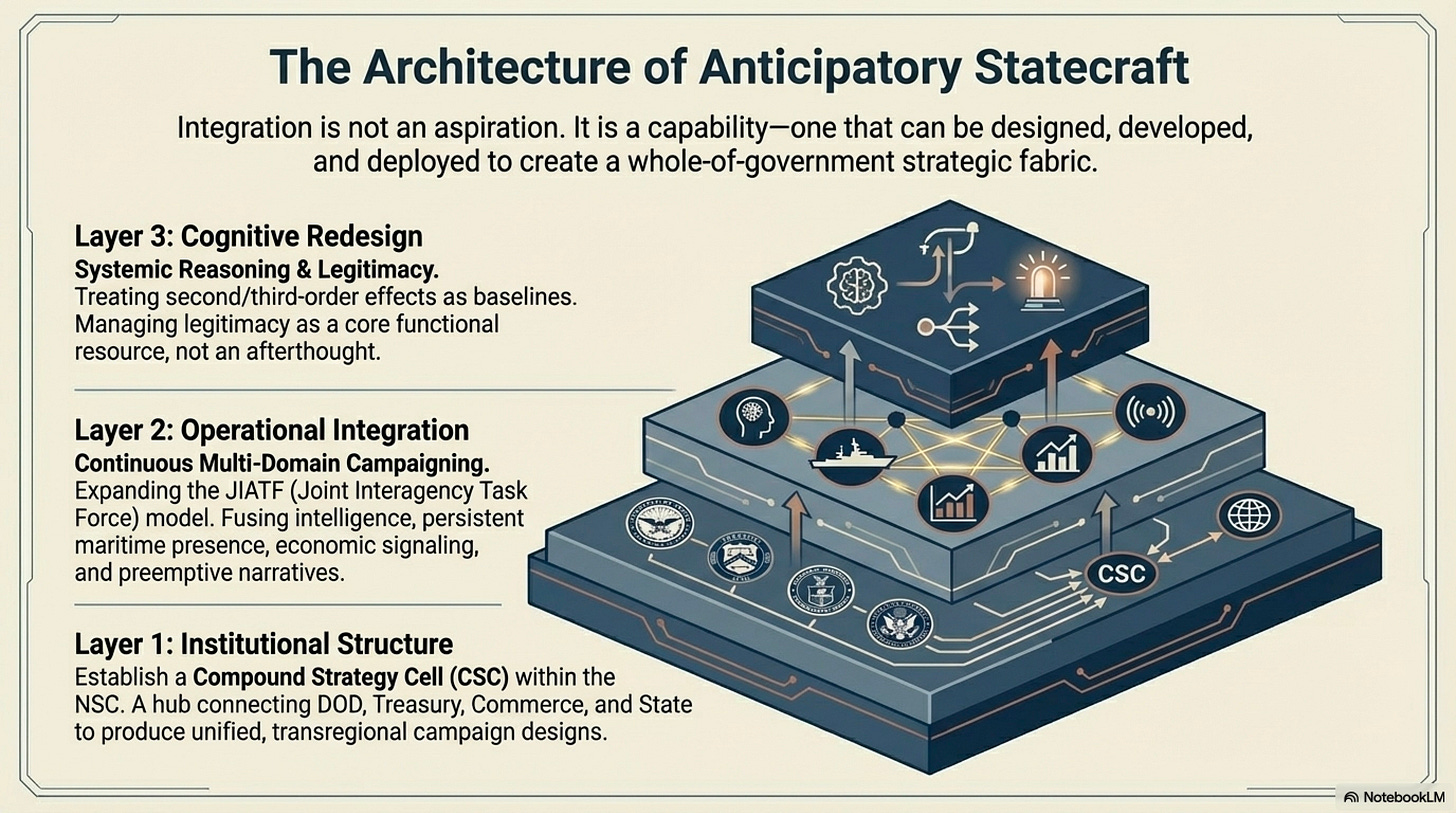
There is, however, a model for such integration. The Joint Interagency Task Force (JIATF), developed during operations in Iraq, demonstrates the potential of a truly integrated approach. By bringing together military, intelligence, and civilian agencies into a unified structure, the JIATF enabled a level of coordination and effectiveness that was otherwise unattainable.
The success of this model lay not simply in cooperation, but in fusion. Intelligence was integrated across sources. Operations were synchronized across domains. Decision-making was accelerated through shared understanding. The result was a capacity to disrupt complex networks through coordinated action, achieving effects that exceeded the sum of individual efforts.
The lesson is clear: integration is not an aspiration. It is a capability—one that can be designed, developed, and deployed.
Toward a Whole-of-Government Strategic Fabric
Building on this insight, the United States must move toward what might be described as a whole-of-government strategic fabric—an integrated architecture that aligns planning, operations, and analysis across domains and agencies. This requires reimagining not only structures, but processes.
Central to this effort is the role of wargaming. Properly conceived, wargaming is not merely a tool for testing plans, but a mechanism for integrating perspectives, identifying interactions, and anticipating outcomes. As recent Department of Defense initiatives have recognized, revitalizing wargaming is essential to navigating a period of rapid change.
Yet wargaming must evolve. It must move beyond isolated scenarios to encompass transregional, multi-domain dynamics. It must integrate interagency and allied participation. And it must be embedded within a continuous cycle of assessment and forecasting, enabling decision-makers to operate with greater foresight and agility.
A Strategic Agenda for the United States
To compete effectively in an age of compound security, the United States must undertake a series of deliberate reforms. It must redesign its strategic architecture to reflect transregional realities, institutionalize integration across agencies and domains, and develop new methods for assessing risk and allocating resources. It must invest in anticipatory capabilities, including emerging technologies that enhance the ability to detect and interpret complex patterns. And it must recognize the centrality of the human domain, treating legitimacy and narrative coherence as core elements of strategy.
These steps are not optional. They are necessary to align U.S. capabilities with the environment in which they must operate.
Conclusion: From Power to Design
The United States retains unparalleled resources and influence. But in a world of compound security, advantage will not accrue to those who possess the most power, but to those who can best integrate and apply it.
The challenge, therefore, is not simply to deter or defeat adversaries, but to design systems that can operate effectively within a complex and interconnected environment. This requires a shift in mindset—from viewing strategy as a sequence of actions to understanding it as a process of shaping systems.
The future of competition will be determined not by who fights the hardest, but by who understands the system most clearly—and who can shape it most effectively.
Author Bio
Dr. Isaiah (Ike) Wilson III is a retired U.S. Army Colonel and former Senior Executive Service (SES) official in the Department of Defense. He is the founder of Wilson W.i.S.E. Consulting LLC and a leading authority on strategic competition, irregular warfare, and compound security. He previously served as President of the Joint Special Operations University and as Professor of Practice at Arizona State University.
References —
Thomas C. Schelling, Arms and Influence (1966).
Isaiah Wilson III, “Compound Security Competition” (2024).
Sun Tzu, The Art of War.
Henry Kissinger, World Order (2014).
Amy B. Zegart, Flawed by Design (2000).
Lawrence Freedman, Command: The Politics of Military Operations (2022).
Kenneth M. Pollack, The Persian Puzzle (2004).
H.R. McMaster, Battlegrounds (2020).
If you value this work, here are three ways you can step into the story with us:
📰 Subscriber (Free)
Stay informed. Receive every new essay, briefing, and analysis straight to your inbox. Join a growing community committed to civic resilience and national security.
🎧 Supporter (Paid Pledge)
Strengthen the signal. Your support sustains both Compound Security, Unlocked and our companion podcast The Civic Brief. Supporters ensure these conversations remain accessible to the wider public while elevating the quality, depth, and reach of the work.
🛡️ Sustainer (Patron Level)
Invest in the mission. Sustainers fuel new research, convenings, and storytelling that enlarge the civic frame of security. This is more than content — it’s a civic project. Your sponsorship helps preserve an independent voice committed to equipping citizens, leaders, and institutions for the compound challenges ahead.